Role-based access control in education systems
Student data visibility is not a configuration choice — it is a governance decision with regulatory consequences. When role-based access control in education systems is designed without clear boundaries, what starts as a flexible pilot setup quickly becomes an audit liability. School districts and institutions reviewing vendor platforms now ask precise questions during procurement: who can see student records, under what permission rules, and what the logs confirm. The access model either answers those questions or it delays the deal.
This article is for CTOs, VPs of Engineering, and IT directors building or deploying education platforms who need their permission models to hold up under institutional compliance review. Next — a practical framework for structuring roles, permission matrices, and logging in alignment with FERPA and COPPA requirements.
Role-based access control (RBAC) in education systems is a structured permission framework that assigns data visibility and action rights according to instructional, administrative, and governance responsibilities, aligned with regulatory obligations. Getting this architecture right reduces audit exposure, simplifies vendor classification under FERPA, and prevents the informal permission drift that compounds across deployment phases.
Teams working through education product development often find that access design is the first question institutional clients raise — before features, pricing, or SLAs.
What makes role-based access control in education different
Most access control frameworks start with a product question: who needs to do what? In edtech, that question arrives downstream of a regulatory one. The Family Educational Rights and Privacy Act (FERPA) defines how student records must be handled and determines whether a vendor qualifies as a "school official" with legitimate educational interest — a classification that governs what data the vendor's system can process and retain.
This means role design in education platforms is not a purely technical decision. It intersects with legal classification, institutional policy, and the specific criteria that procurement officers use during evaluation. Vendors building for edtech platform engineering know that the access model is frequently reviewed before the feature set, particularly when the client is a K-12 district with its own legal and compliance team.
The three governance questions every role must answer
Before any role is deployed in a learning system, it needs explicit answers to three questions:
- What data is this role permitted to see? - Define scope: own-class only, district-wide, anonymised vs. identifiable.
- What actions is this role permitted to take? - View, edit, export, and administrative actions should be specified separately.
- What events does this role trigger in the audit log? - Every permission-sensitive action should generate a traceable record.
If any of these three is undefined — or answered informally — the role is incomplete. That gap may not cause immediate problems, but it will surface during a compliance review or during incident investigation when someone needs to explain what a particular user accessed and why.
How pilot phases create access drift — and how to stop it
Pilot deployments are where access models most often break down. The dynamics are predictable: teams need to validate functionality quickly, so permissions are widened to remove blockers. Temporary access gets granted without expiration rules. Reporting and instructional roles get merged for convenience. By the end of the pilot, the access model reflects test conditions rather than production governance requirements — and rolling it back is politically and technically harder than it should be.
Specific patterns that appear across almost every pilot phase:
- Full district role hierarchies replicated for a single-school validation scope
- Developer access granted to production environments without defined expiration
- Broad data visibility enabled 'for testing purposes' without scope limits
- No separation between staging and production environments for access control purposes
These decisions compound. Once a role has been assigned and used, reducing it requires justification and often generates internal resistance. Access that was granted for convenience becomes access that teams expect to keep. Pilot containment strategies for edtech address exactly this problem — how to structure a validation phase that does not accumulate governance debt before the product reaches production.
Designing permission matrices that hold up under procurement review
Permission matrices are where access design moves from policy to specification. A matrix forces every role into a concrete form: what it can view, what it can edit, what it can export, and what administrative actions it can perform. Without this structure, roles exist as general descriptions that mean different things to different stakeholders — and those interpretations diverge precisely when they matter most.
The practical value of a permission matrix is that it becomes a shared artifact. Technical teams, school administrators, and institutional compliance reviewers can examine the same document and verify alignment. During procurement, districts often request the access model directly — not a description of the approach, but the model itself in a reviewable format.
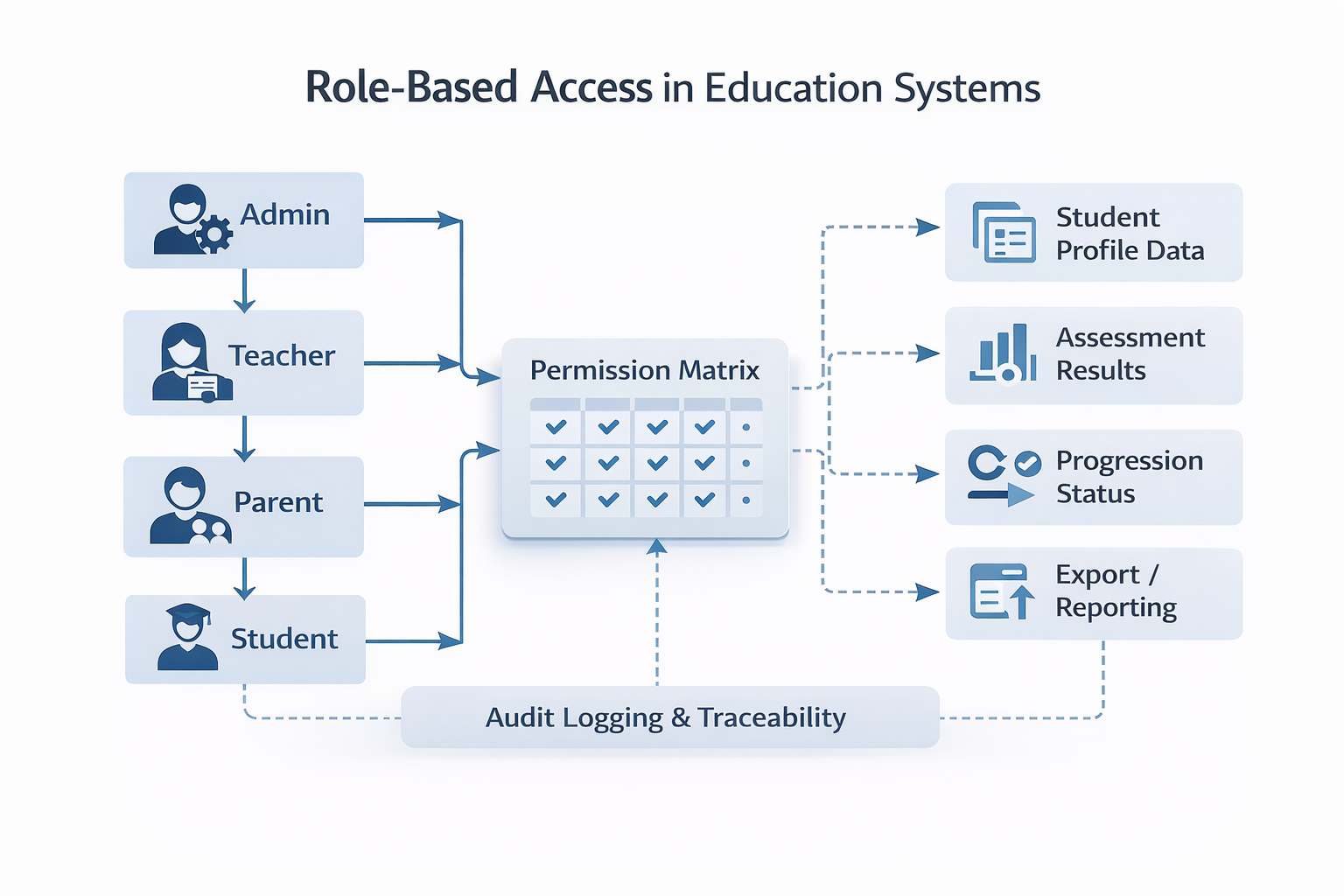
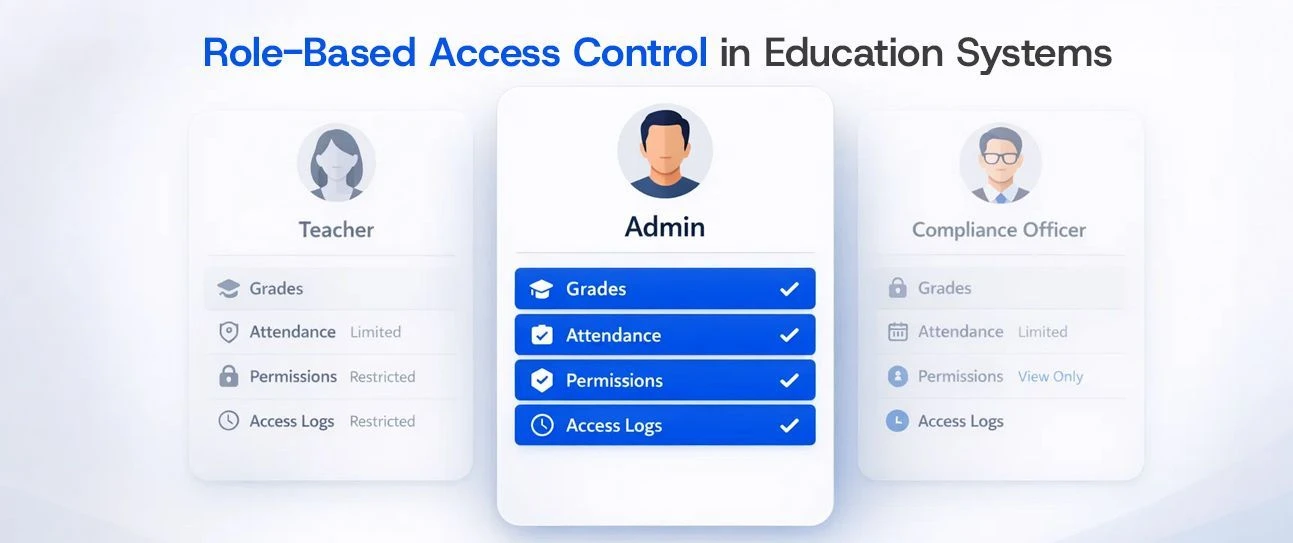
role-based-access-education-systems-architecture
Figure 1: Permission matrix showing RBAC scope across teacher, administrator, and district roles in an education platform. Explicit matrices make role boundaries reviewable by both technical teams and institutional compliance officers.
Core dimensions of an education permission matrix
The table below outlines the standard permission types and how they map to role scope in a regulated education environment:
Table 1: Education permission matrix — standard dimensions and role assignment examples for RBAC in regulated learning environments.
If your team is now defining access boundaries for an education platform — whether ahead of a pilot launch or before a district procurement review — the moment to structure roles correctly is before the first user is onboarded, not after the first audit question arrives. Our engineers can map your access model to institutional requirements directly. Discuss your access architecture with Bluepes.
Data minimization as a structural constraint, not a preference
The standard framing of data minimization is regulatory: give users only the data they need for their defined purpose. That framing is accurate, but it underestimates how much the principle changes the design process. Data minimization is not a filter applied at the end of access design — it is the starting constraint that determines what gets built into the permission model at all.
In practice, this means questioning every data element a role can access and requiring a specific justification for its inclusion. If the justification is 'it might be useful' or 'it's easier to show everything', the answer should be no. Purpose-based visibility is harder to build initially and significantly easier to defend during audits and institutional review.
FERPA, COPPA, and what they actually require from access design
FERPA requires that vendors handling student records establish a legitimate educational purpose for each data access point and that institutions retain oversight of what data is shared and with whom. The practical consequence is that role definitions must map to specific instructional or administrative functions — not to general-purpose access for technical teams.
The FTC COPPA rule applies to platforms serving users under 13 and adds specific obligations around data collection limits and parental consent mechanisms. For K-5 platforms, this means roles must be designed to prevent incidental exposure of data that the platform has no legitimate basis to collect in the first place. Neither regulation specifies a particular access model, but both create conditions under which an overprovisioned model becomes a legal liability rather than simply a governance issue.
K-5, K-12, and higher education: why one access model doesn't fit all
Generic RBAC templates create problems because the institutional structures they try to represent are genuinely different from each other. An access model designed for a K-12 district will have the wrong structural assumptions built in if applied to a single K-5 school — and both will be wrong for a higher education context where academic departments operate with significant autonomy. The differences are not superficial.
The instructional orchestration model in education platforms documents how these structural differences translate into concrete product decisions, including how access and role boundaries should be defined at each level.
- K-5 environments keep roles tightly scoped to classroom context. Teachers access only their own class data. Parental visibility is a specific, bounded role rather than a subset of administrative access. Administrative layers are minimal, and cross-department data flows are rare.
- K-12 districts require role hierarchies that span multiple schools, with school-level administrators, district IT oversight, and centralized reporting structures. Compliance review is more formal, and role definitions must enforce data segregation between schools operating under the same district.
- Higher education introduces department-level autonomy, faculty override authority, multi-course access patterns, and integration with student information systems (SIS) and academic records systems. Permission models must reflect academic governance structures — not just administrative hierarchy.
Applying the wrong template to any of these contexts does not just produce usability friction. It produces access models that either over-expose data or under-support legitimate use — both of which require redesign under institutional pressure, typically at the worst possible time.
Controlled vs expanded access: what the difference looks like in practice
The following comparison describes how the two approaches diverge across key governance dimensions. The gap typically becomes visible during a procurement review or after an audit — not during initial deployment.
Table 2: Controlled vs expanded access model — governance and procurement impact comparison.
Logging and audit traceability: making access control operational
Access control design is incomplete without logging. A permission matrix defines what should happen. Logs record what actually happened. Without that second layer, access control exists as policy but cannot be verified, enforced, or explained in practice — which is exactly what institutional reviewers check.
What gets logged is a design decision, not a configuration afterthought. The minimum that any regulated education environment should capture includes: authentication events (login, logout, failed attempts); permission changes (role assignment, escalation, revocation); data export events (what was exported, by which role, at what time); override actions (who approved an exception and what data it affected); and anomalous access patterns (access outside defined scope or beyond expected hours).
These logs serve three distinct functions. Day-to-day, they support operational monitoring. During audits, they provide the evidence trail that institutional reviewers require to sign off. During incidents, they are the forensic record that determines whether an investigation takes hours or weeks. Cybersecurity services for education platforms typically include logging architecture as a core component, particularly where platforms need to demonstrate compliance readiness before institutional go-live.
The NIST SP 800-53 access control framework provides the technical standard that government-affiliated and regulated education environments reference for audit and logging requirements. Formal NIST compliance is not always required, but using that framework as a design reference prevents the most common gaps that show up in institutional reviews.
Infrastructure ownership and access architecture alignment
Role definitions do not exist independently of infrastructure decisions. When a district requires that production student data be stored in school-controlled infrastructure or an approved cloud account, the access model must enforce that boundary. Developer access to production environments, export permissions, and cross-environment visibility all need to be explicitly scoped — and documented separately from the general permission matrix.
Common misalignments that surface during procurement reviews: developers retaining read access to production student data after go-live; export permissions that do not distinguish between anonymised and personally identifiable records; staging environments that operate on real student data without restricted access controls. Each creates a gap between what the vendor's documentation describes and what the technical configuration actually permits.
That gap is precisely what district compliance reviewers examine. Role architecture must align with hosting architecture — these are not separate decisions made by separate teams at separate times. Building that alignment in from the start is consistently faster than reconciling it under procurement pressure.
Key takeaways
- Role-based access control in education systems is a regulatory and governance requirement, not a product feature decision that can be deferred to a later sprint.
- Pilot phases are the most common source of access drift — define scope boundaries before the first user is onboarded, not after the first audit question arrives.
- A permission matrix is the primary artifact that connects access design to institutional procurement review criteria.
- Data minimization means starting from what is required for each role's defined function — not filtering from what the system makes available by default.
- Logging makes access control operational. Without it, the permission model cannot be verified, enforced, or used in incident investigation.
- Access architecture must align with hosting and infrastructure decisions — role design and environment design are the same project.
Getting access architecture right before procurement, not after
Access design in education platforms shapes more than operational behavior. It determines how institutional clients evaluate the product, how quickly procurement clears, and how exposed the institution is when something goes wrong. Getting the permission model correct during the design phase takes time. Correcting it after a district compliance officer has flagged a concern takes significantly more — and often delays deals that were otherwise close to closing.
The patterns described in this article — pilot access drift, permission matrix gaps, incomplete logging, misaligned infrastructure boundaries — appear consistently across edtech vendor engagements. They are not unique failures. They are structural tendencies that emerge when access design is treated as a secondary task rather than a primary architectural decision.
If you are preparing an access model for an education platform and want a review before the first institutional client engagement, schedule a structured access architecture review with Bluepes.
FAQ
Interesting For You

Instructional Orchestration vs. Software Automation in Regulated Education Systems
Instructional orchestration defines how learning sequences, mastery rules, and teacher intervention logic are structured within a digital system. Automation alone does not guarantee pedagogical alignment; orchestration requires mapping educational theory to system behavior. In K–5 and K–12 environments, sequencing logic directly affects learning progression, while in higher education it impacts curriculum pathways and credit logic. This article explains how mastery modeling, teacher override controls, and system constraints intersect in regulated learning environments. It is relevant for instructional designers, academic technology teams, and EdTech product leaders building structured learning systems.
Read article

Why Most EdTech Pilots Fail: Designing a Contained Learning Path Pilot in Regulated Education
A contained learning path pilot is a structured, limited-scope validation phase designed to test instructional logic, sequencing rules, and mastery criteria without building a full production system. In K–5, K–12, and higher education environments, pilot containment reduces instructional and technical risk while preserving architectural clarity for future scaling. Overextending early pilots often increases adoption friction and governance complexity. This article explains how to define pilot scope, isolate variables, and align validation metrics with long-term system strategy. It is relevant for school leaders, EdTech founders, curriculum architects, and technology directors evaluating instructional pilots.
Read article

EdTech batch integration architecture
Many education platforms operate without real-time APIs and rely on structured exports such as CSV files for data exchange. Reliable learning logic in these environments requires deterministic batch processing, normalization rules, and clearly defined synchronization windows. System behavior must account for delayed updates, reconciliation logic, and audit traceability. This article explains how to design integrations for K–12 and higher education systems when near-real-time connectivity is unavailable. It is relevant for integration architects, district IT teams, and vendors working with legacy or closed educational platforms.
Read article