BluePes Blog: Insights & Trends
E-commerce RFP technical questions vendors must answer
This article gives eight questions worth adding to an e-commerce development RFP and explains what a strong answer, a weak answer, and a direct Bluepes-style answer should look like.
- May 29, 2026
- 16 min
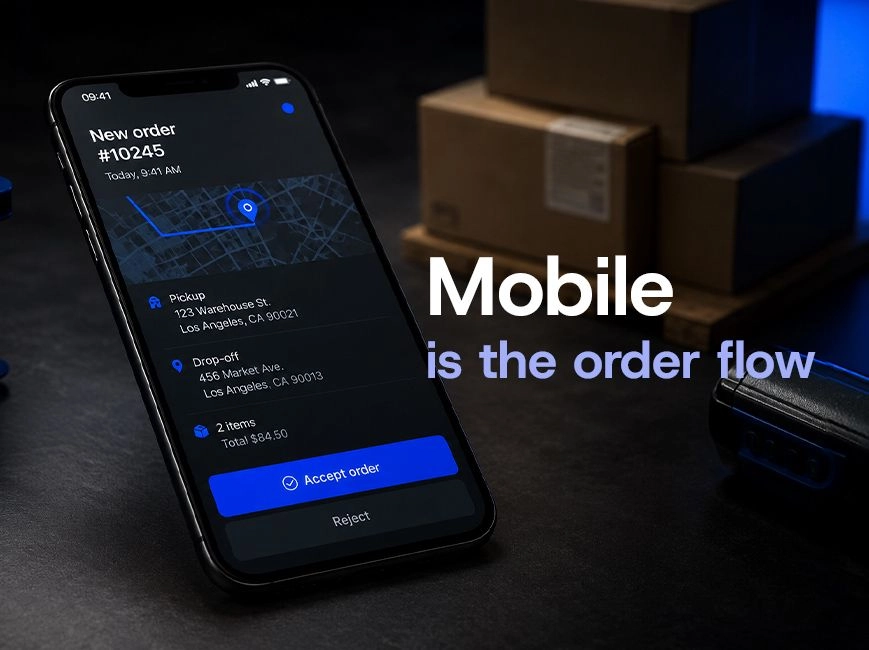
Supplier mobile app for marketplaces: a decision guide
For marketplace teams with a functioning supplier dashboard, the next decision is whether to extend it with a mobile experience and what shape that mobile product should take. The reader of this piece already has operational evidence on where vendors fall out of the flow. The question is whether a supplier mobile app for marketplaces is worth the engineering investment, and which architectural decisions matter most if the answer is yes.
- May 28, 2026
- 16 min

Location-based order routing: where geo-routing breaks
Location-based order routing is an architectural choice that touches four systems at once — supplier registry, inventory visibility, pricing logic, and customer-facing UX. The routing algorithm itself is usually the smallest part of the work. Most marketplaces hit this point when delivery cost starts to dominate the customer's experience of the platform.
- May 22, 2026
- 15 min

Marketplace plugin vs purpose-built platform: when to move
Marketplace plugin vs purpose-built platform is not a feature comparison. A plugin is an adapter over someone else's commerce architecture. At low volume the adapter holds. As the operating model grows — multi-jurisdiction payouts, custom routing, per-vendor pricing and inventory variation — the gap between what the plugin allows and what the business needs widens into operational cost. At that point the architecture decides the next eighteen months of the business, not the feature roadmap.
- May 15, 2026
- 15 min

Why Your ERP Integration Fails Silently Under Load
These ERP integration failures are the most expensive category of integration problem in e-commerce because they don’t generate tickets or on-call pages. They surface as accounting discrepancies weeks after the data diverged, when the cost of diagnosis and correction has already multiplied. Almost always, they trace back to four architectural decisions that were either made implicitly or not made at all when the integration first went live: field-level data ownership, sync model selection per data type, bidirectional idempotency, and pre-incident observability. Each gap is diagnosable in a running integration, and each has a fix that does not require a full rewrite.
- May 08, 2026
- 15 min

Why Small BI Projects Fail Before They Even Start
The core issue sits below execution — in the gap between what the project was scoped to deliver and what the data environment actually requires. A dashboard looks like a reporting deliverable. Behind it sits a chain of decisions about data ingestion, transformation, modeling, access control, and refresh scheduling. Underscope any one of those layers, and the project either stalls mid-delivery or produces output nobody trusts enough to act on.
- Apr 30, 2026
- 16 min
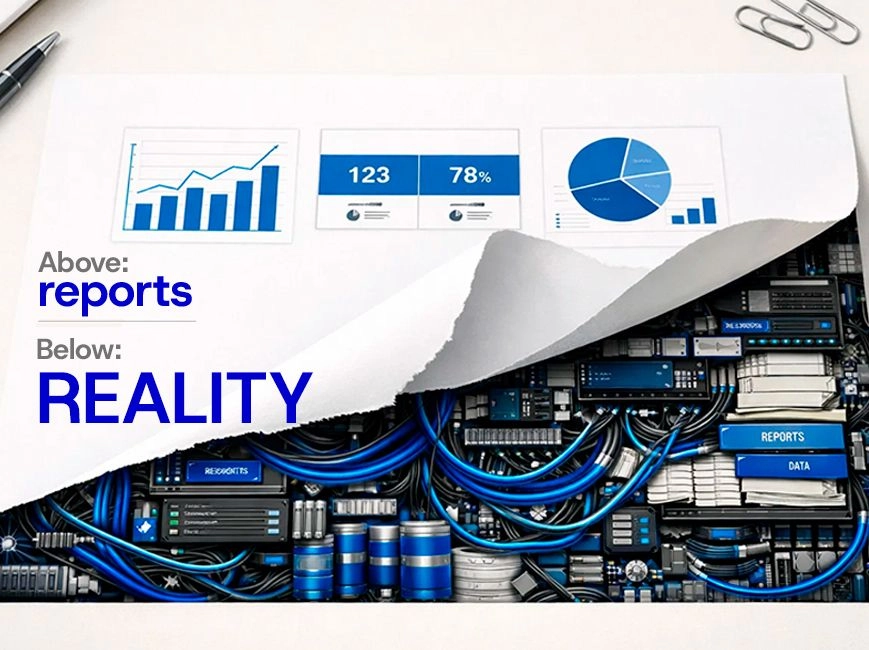
BI project estimation starts before the first dashboard
The short answer: most BI scoping underestimates happen because the client sees the reporting layer and nobody maps what feeds it. Data ingestion, storage, and transformation aren't optional add-ons — they're the foundation. When they don't exist, the project scope changes. Not because the vendor is inflating the work, but because the work was always there.
- Apr 24, 2026
- 15 min

Power BI developer vs data engineer: who comes first
A Power BI developer specialises in visualisation, data modelling inside Power BI, and report logic. They do not build data pipelines or transform raw data from complex sources. Without a clean, prepared data layer in place, there is nothing for them to work with — and no amount of experience changes that constraint. The decision that determines project success is not who you hire, but what is already ready when they start.
- Apr 17, 2026
- 16 min

Education data privacy requirements in the US and Europe for software
Education data privacy requirements create binding architectural constraints the moment a vendor touches a student record. FERPA, COPPA, state statutes, and GDPR each impose distinct obligations — on access design, data retention, sub-processor management, and deletion logic — and they frequently apply to the same system at the same time. This article is for IT directors, CTOs, and compliance leads at edtech vendors and school districts who are building or procuring student-facing platforms across U.S. and European markets. If your system stores, processes, or transmits student data in either jurisdiction, what follows maps the legal obligations directly to the technical decisions you need to make. The short answer: U.S. frameworks (primarily FERPA and state laws) focus on institutional control over disclosure and vendor accountability. GDPR centers on individual rights and enforceable technical measures. Both require compliance to be visible in system behavior — not policy documents. The architectural patterns that satisfy one framework partially overlap with the other, but the gaps matter and have caused failed procurement reviews.
- Apr 13, 2026
- 15 min