When Systems Look Stable but Operations Keep Fixing Things: The Hidden Cost of Limited Integration Visibility
This article is relevant for CTOs, operations leaders, integration architects, and finance teams responsible for system interoperability and workflow reliability.
In many organisations, integrations are considered reliable because they rarely fail in visible ways. Interfaces respond, data is exchanged, and monitoring dashboards do not show critical alerts. Yet operational teams still spend time reviewing exceptions, correcting records, and confirming that business steps completed as intended.
The discrepancy becomes apparent when process outcomes are examined rather than technical signals. A workflow may execute without triggering an error while still producing incomplete or delayed results. Over time, this pattern creates operational overhead that is not visible in infrastructure metrics.
This article examines why technical monitoring alone does not provide sufficient assurance for business processes and outlines practical approaches to improving integration visibility.
Technical Health and Business Completion Are Different Signals
Most monitoring setups focus on infrastructure and message flow:
- API availability
- message delivery status
- job execution logs
- system uptime
These checks confirm that components are responsive. They do not confirm that a business workflow reached its intended end state.
For example, an order transmitted from System A to System B may be acknowledged successfully. However, downstream validation logic, sequencing rules, or retry behaviour can alter the final state without producing a system-level failure.
Industry guidance on distributed system observability emphasises this distinction. Martin Fowler’s analysis of observability in distributed systems highlights that monitoring must allow teams to understand behaviour, not only component health.
Similarly, AWS documentation on modern integration and event-driven architectures explains that delivery confirmation does not equate to business-level completion.
These principles apply directly to integration-heavy environments.

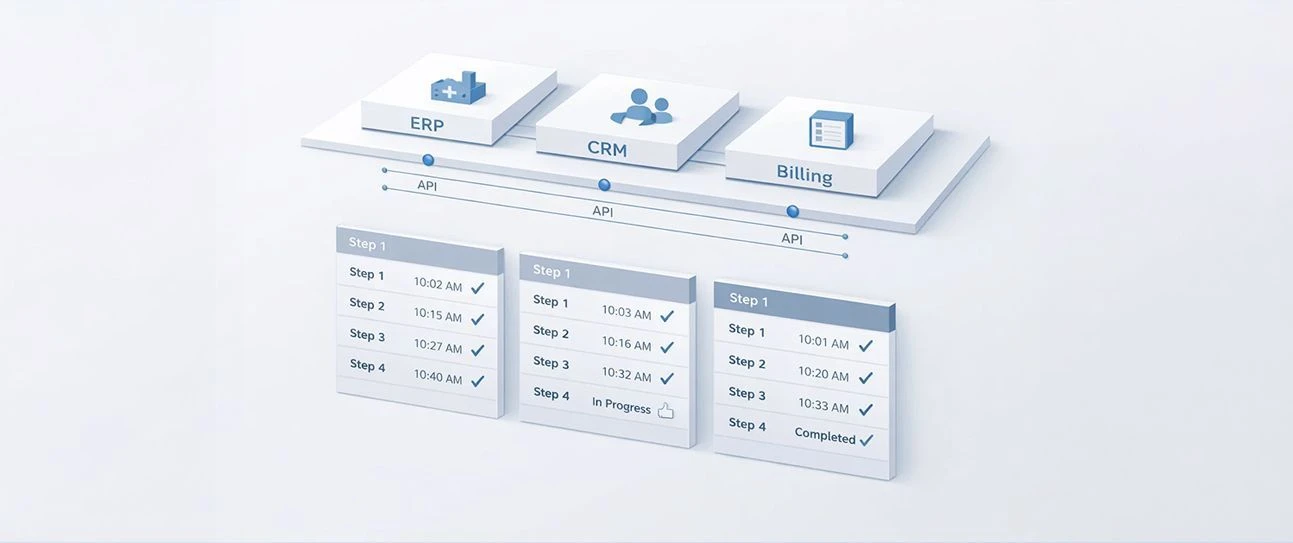
process-level-observability-integration-visibility
Where Manual Intervention Becomes Structural
Operational teams often absorb visibility gaps through manual controls:
- reviewing reconciliation reports
- validating cross-system status alignment
- adjusting records after partial updates
- tracking timing discrepancies outside core systems
At first, these actions are treated as precautionary measures. Over time, they become embedded in daily routines. The integration layer remains technically stable, but process reliability depends on human oversight.
This pattern increases operational cost and reduces scalability. As transaction volumes grow, the same structural limitation requires more supervision.
Process-level observability
Process-level observability refers to the ability to monitor and validate whether a business workflow has completed correctly across all involved systems, including order, timing, and downstream dependencies.
It goes beyond message delivery and infrastructure status. It focuses on verifying outcomes.
Key questions include:
- Did the workflow complete all required steps?
- Were dependent updates executed in the intended sequence?
- Did retries or delays affect final state?
- Is the data consistent across systems after completion?
Without this layer of visibility, organisations discover issues indirectly — through reconciliation, reporting anomalies, or operational review.
Common Visibility Gaps in Integration Monitoring
Organisations typically invest heavily in the left column. The operational impact accumulates in the right.
Growth Exposes Structural Weakness
As system landscapes expand:
- additional platforms are connected
- business rules evolve
- timing dependencies increase
- regulatory and reporting requirements tighten
Sequencing and retry behaviours that were manageable at lower scale begin to affect financial and operational outcomes. What previously required occasional review becomes a recurring operational task.
Integration visibility becomes a governance concern because workflow ownership is often distributed across teams and systems.
If operational teams compensate for technically “healthy” integrations through manual checks and reconciliation, Bluepes can assess where workflow visibility breaks down and how to introduce structured monitoring at the process level.
Learn more about our Integration Consulting services or contact Bluepes to review your current integration landscape.
Technical Monitoring vs Process-Level Observability
Organisations often assume that if integrations are monitored, they are controlled. In practice, most monitoring frameworks answer technical questions but do not validate business outcomes.
Technical monitoring ensures systems are responsive. Process-level observability verifies that business operations complete correctly.
Both are necessary. Only one addresses operational risk.
Implementation Patterns in Integration-Heavy Environments
Introducing process-level visibility requires structural adjustments, not just additional alerts.
Common patterns include:
1. Workflow State Tracking
Tracking lifecycle states explicitly across systems rather than relying on individual platform statuses.
2. End-to-End Correlation IDs
Using correlation identifiers to follow transactions across multiple services and detect partial completion.
3. Sequence Validation Rules
Validating whether steps occurred in the intended order before marking a workflow as complete.
4. Business-Level Monitoring Events
Generating monitoring signals tied to business milestones instead of transport events.
Modern iPaaS platforms support orchestration and visibility features that make these patterns easier to implement. For organisations evaluating integration architecture, structured orchestration through platforms such as Boomi can reduce fragmentation in monitoring logic. Learn more about our Integration Consulting services if you are reviewing your integration architecture.
Structural Constraints to Consider
Process-level observability is not implemented in isolation. Constraints typically include:
- Legacy systems that do not expose consistent state models
- Multiple vendors controlling parts of the workflow
- Inconsistent data schemas across platforms
- Lack of clearly defined workflow ownership
- Organisational silos between IT and operations
These constraints often explain why monitoring remains infrastructure-focused. Visibility across workflows requires cross-functional alignment.
Gartner’s governance research highlights that distributed ownership without structured oversight increases operational risk as complexity grows.
Steps to Introduce Structured Process Visibility
- Identify critical workflows - Focus on processes tied to revenue, financial reporting, or regulatory exposure.
- Map end-to-end dependencies - Document which systems participate and in what sequence.
- Define expected completion states - Establish what “correct” means for each workflow.
- Introduce correlation tracking - Ensure transactions can be traced across systems.
- Monitor deviations, not just failures - Detect delays, sequencing issues, and partial updates.
- Assign workflow ownership - Make responsibility explicit.
This work often overlaps with broader data and governance initiatives. Organisations reviewing cross-system reliability frequently address it alongside Data & Analytics Consulting initiatives to align reporting and operational visibility.
Conclusion
Technical monitoring provides assurance that systems are available and responsive. Process-level observability provides assurance that business workflows complete correctly across interconnected platforms. As system landscapes expand, the gap between these two layers becomes more visible through manual corrections, reconciliation effort, and growing operational oversight.
Organisations that depend on cross-system workflows should evaluate whether monitoring covers business outcomes or only component status. When workflow validation is embedded into integration architecture, operational stability improves and manual intervention decreases over time.
If your organisation relies on integrations that appear technically stable yet require ongoing operational supervision, it may be time to assess workflow visibility at the architectural level. Bluepes works with integration-heavy environments to analyse process behaviour across systems, identify sequencing and timing gaps, and design structured observability approaches aligned with business outcomes.
FAQ
Interesting For You

KPI misalignment across teams: the structural causes
KPI misalignment is the condition where the same metric carries different definitions across teams, so each one produces a defensible but different value. The cause usually sits in how metrics were introduced, defined, and copied across systems over time. The conflict only becomes visible — and expensive — when those numbers meet in a shared decision.
Read article

How financial data becomes inconsistent — and what structured integration solves
Financial systems rarely break in obvious ways. Payments are processed, accounting entries appear, data moves from one platform to another. The problem surfaces later — when finance teams prepare month-end reconciliations, quarterly reports, or audit packages and find that figures from the accounting platform, the payment provider, and the BI tool do not agree. This article is for CFOs, finance operations leads, and IT directors at mid-market companies who have connected multiple financial systems but still spend significant time reconciling data before each close. Next — a structured explanation of why inconsistencies happen and which integration approaches reduce them. Financial data inconsistencies are not random. They follow predictable patterns related to event timing, partial updates, and the absence of coordinated flow logic. Structured integration using a centralized iPaaS layer addresses these patterns directly and reduces the operational cost of managing finance data across systems.
Read article
How to Monitor Distributed Systems and Manage Failure Models
Distributed system monitoring is the combination of telemetry collection — metrics, traces, and logs — with failure-aware alerting that lets engineering teams detect, diagnose, and resolve problems spread across interdependent services. The teams that get this right design their monitoring around specific failure models, and they pay attention to alert quality, not just alert volume. The payoff is significant: incident diagnosis drops from hours to minutes, and each failure stays contained instead of cascading.
Read article