How to structure healthcare system integration across EHR, labs, billing, and analytics
Healthcare IT teams deal with one of the more unforgiving integration environments in enterprise software. Systems must stay connected around the clock, data failures carry real clinical and financial consequences, and the architecture that worked at 50,000 transactions a month often starts breaking silently at 500,000.
This article is for CTOs, IT directors, and VP-level engineering leaders in healthcare organizations who are responsible for keeping EHR, lab, billing, and analytics systems aligned — especially when those systems were not designed to work together. The focus here is on architecture: what breaks, why it breaks, and how a centralized integration layer changes the outcome.
Healthcare system integration — the structured exchange of data between clinical, operational, and analytical platforms — is not a one-time project. It is a continuous operational responsibility. The organizations that get it right invest in architecture before they need it, not after the first major incident.
Bluepes is an independent software consulting company that works with Boomi and other integration technologies to help healthcare organizations build and maintain robust integration layers. Our healthcare integration projects have consistently shown that fragmentation is not the root problem — unmanaged fragmentation is.
Updated in April 2026
The reality of a typical healthcare system landscape
A healthcare integration platform — that is, a managed layer through which disparate clinical and operational systems exchange data — is not standard across the industry. Many organizations run on a mix of point-to-point connections built at different times, by different teams, with different error handling assumptions.
The common system categories in play are:
- Electronic Health Records (EHR / EMR)
- Laboratory Information Systems (LIS)
- Billing and claims platforms
- Insurance eligibility and clearinghouse services
- Business intelligence and analytics tools
Each of these evolves on its own vendor roadmap. Regulatory changes affect EHRs on one timeline; billing system updates follow payer requirement changes; lab platforms release new connectors according to their own cycles. Nothing synchronizes automatically, which means integration logic written six months ago may no longer reflect current data models.
Fragmentation itself is not unusual. What creates operational risk is when integrations are built as isolated connections with no centralized oversight — no shared error handling, no consistent logging, no way to observe what is actually moving between systems.
Where integration friction starts — and why it is hard to see
Friction in healthcare data integration usually comes from a mismatch in system priorities, not from technical failures. Clinical systems are built for accuracy and completeness. Billing systems prioritize reconciliation and timing. Insurance services depend on external validation cycles. Analytics platforms need clean, structured, consistent datasets. None of these goals conflict by design — but they come apart under load or after system updates.
Standards like HL7 FHIR help normalize how healthcare data is represented and exchanged through APIs. They reduce transformation complexity significantly. What they do not solve is orchestration: the sequencing of steps, retry logic on partial failures, conditional routing when downstream systems are temporarily unavailable, and change management when any system in the chain gets updated.
Research from HIMSS on healthcare interoperability consistently describes interoperability as an ongoing operational responsibility — not something that gets checked off after initial implementation. That framing matches what engineering teams actually experience.
Common integration challenges by system type
Individually, each of these challenges is manageable. The problem compounds when all five systems must stay synchronized, and any one of them changes.
Why point-to-point integrations fail at scale
Point-to-point connections are the default choice when integration needs arise one at a time. They are fast to build and easy to reason about — two systems, one connection, clear ownership. Their failure mode only becomes visible as the environment grows.
Each new connection adds to a dependency graph that nobody fully owns. A change in one system's API or data model may silently break several downstream integrations. Errors are often caught not by monitoring but by clinical or billing staff noticing inconsistencies in reports or records — which means the failure already had real impact before it was detected.
The patterns that accumulate over time:
- Integration logic embedded directly in source systems, making it hard to trace or update
- Inconsistent error handling — some connections retry, others drop data silently
- No centralized visibility into which data flows are healthy and which are not
- Institutional knowledge held by specific developers rather than documented in the architecture
This accumulation is what engineers refer to as integration technical debt — the gap between what the integration layer was designed to handle and what it actually has to handle now. The debt does not create a single failure. It creates a pattern of recurring small failures that are expensive to diagnose and impossible to prevent without architectural change.
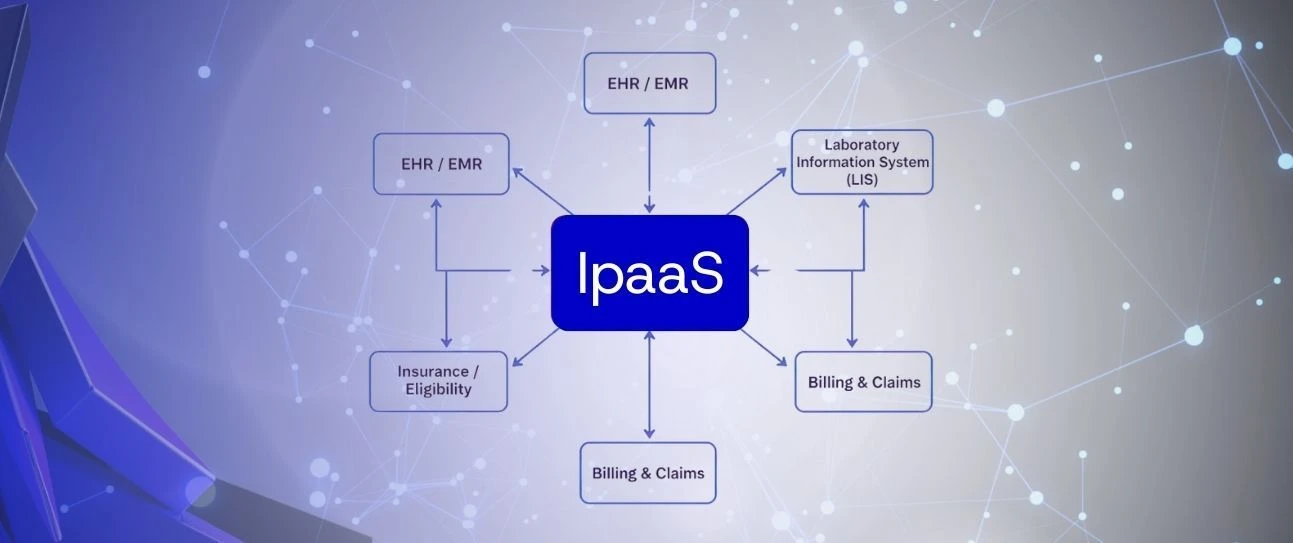
iPaaS as a healthcare integration control layer
An Integration Platform as a Service (iPaaS) addresses this by moving integration logic out of individual systems and into a managed, centralized layer. Instead of building and maintaining connection-specific code across every system pair, integrations are defined as reusable processes that run through a single platform with shared monitoring, error handling, and change management.
That layer typically handles:
- Data mapping and transformation between system formats
- Multi-step workflow orchestration with conditional logic
- Retry and error handling for partial failures
- End-to-end process monitoring and centralized logging
- Controlled deployment of changes across environments
Our clients in healthcare choose to work with Boomi as their iPaaS layer primarily for two reasons: the visual process designer reduces the time to build and modify integrations, and the Atom deployment model allows processes to run on-premises or in cloud infrastructure without exposing patient data to external systems. For regulated environments, that flexibility matters.

healthcare-ipaas-integration-layer-diagram
If your organization is running integrations that grew over time without a centralized architecture, the risk tends to be invisible until something breaks at the wrong moment. Teams that have already built this in healthcare have found that reviewing the current integration structure before a platform migration or system upgrade saves several weeks of emergency rework. Discuss your architecture with the Bluepes team — or explore what a dedicated integration team engagement looks like for your environment.
Practical integration patterns across EHR, labs, billing, and analytics
Healthcare integrations rarely run as simple one-to-one connections in production. Most clinical workflows require multiple systems to react to the same event — and to react in a specific order, with recovery logic if any step fails.
EHR-driven event flows
When a patient encounter is created or updated in the EHR, downstream systems need to act: billing needs the encounter data to initiate a claim, insurance validation runs against eligibility records, and analytics platforms need the structured data for reporting. Each of these is a separate process with its own timing, format requirements, and failure modes.
Without orchestration, this fan-out either happens synchronously (creating latency in clinical workflows) or through separate point-to-point connections (with no shared error visibility). A centralized integration process handles the sequencing, formats the data for each target, and manages retries without coupling the EHR to any individual downstream system.
Lab result distribution
Lab results carry time-sensitivity that most other data exchanges do not. A result that arrives 40 minutes late, or arrives in the EHR but not the reporting platform, creates both clinical and compliance exposure. Partial delivery — where results reach some systems but not others — is harder to detect than complete failure.
The integration pattern here requires event-driven triggering (the LIS publishes the result as an event), structured delivery to multiple targets, and confirmation logic that verifies receipt before marking the process complete. Our healthcare platform integration case involved exactly this pattern across multiple clinical systems — the primary engineering challenge was not the data mapping but the delivery confirmation and partial-failure recovery.
Connecting BI and analytics
Analytics platforms have a different integration requirement: they need consistent, complete, and correctly structured datasets — not just the latest event. Any inconsistency in how clinical data was captured, transformed, or delivered upstream will appear in reports as data quality issues that are difficult to trace back to their source.
Structuring analytics integrations through a central layer means transformations are defined once, applied consistently, and auditable. Changes to source data models do not silently break report accuracy — they trigger alerts at the integration layer, not after the fact in a dashboard. For teams managing financial data integration consistency, this is the same principle applied across a different data domain.
How monitoring and traceability reduce operational risk
One of the most consistent gaps in healthcare integration environments is observability. Many failures are not system outages — they are silent degradations where data arrives late, partially, or inconsistently without triggering any alert. Teams discover them through reporting discrepancies or from clinical staff flagging missing records.
Effective integration architectures include monitoring that is built around operational impact, not just technical status. That means:
- End-to-end process monitoring that tracks a message from source to all destinations
- Centralized logging with enough detail to reconstruct what happened for any individual transaction
- Error classification that distinguishes between data issues, system unavailability, and configuration errors
- Alerting thresholds calibrated to clinical and billing workflows, not just infrastructure metrics
Without this, engineering teams spend disproportionate time on reactive diagnosis. With it, the same team can maintain a much larger integration surface with confidence. Integration observability in healthcare workflows covers the specific patterns and tooling choices in more detail.
Managing change without breaking existing integrations
Healthcare systems are updated continuously. EHR vendors release quarterly updates; billing formats change with regulatory cycles; insurance APIs evolve with payer requirements. Each update is a potential integration failure if the architecture does not account for change management.
The most fragile architectures are those where integration logic is tightly coupled to specific data model versions. A field name change in the EHR breaks downstream transformations. An updated billing schema causes rejected claims. These failures are not rare edge cases — they are predictable outcomes of an architecture without isolation layers.
A centralized integration layer separates the interface each system sees from the internal data models it uses. When the EHR updates its patient record structure, only the integration mapping changes — not every downstream system that consumes patient data. This isolation is what makes the architecture sustainable over time, not just at initial deployment.
The practical implication: integration testing should be part of every system update cycle, not just initial implementation. Teams that manage this well treat their integration layer as a product that requires its own maintenance budget and ownership — not as infrastructure that runs in the background without attention.
Key takeaways
- Healthcare system integration is an ongoing operational responsibility — not a project with a completion date.
- Point-to-point connections accumulate integration technical debt that creates predictable failure patterns at scale.
- An iPaaS layer centralizes orchestration, error handling, monitoring, and change management across all system connections.
- HL7 FHIR standardizes data representation, but orchestration and change isolation still require a dedicated integration platform.
- Observability — end-to-end process tracking and alerting — is the difference between discovering failures from reports and catching them before they have clinical or financial impact.
Conclusion
The question healthcare engineering teams usually arrive at is not whether to restructure their integration architecture — it is when. The answer is almost always: before the next major system migration, not during it.
A centralized integration layer built on a platform like Boomi changes the operational dynamic for organizations running multiple clinical and operational systems. It moves integration from a collection of individual connections that each need separate attention to a managed layer that can be monitored, tested, and updated with a consistent approach.
Bluepes works with healthcare organizations as an independent integrator — designing, building, and maintaining integration architectures that hold up as systems scale and requirements change.
If you are planning a platform migration, evaluating your current integration structure, or dealing with recurring data quality issues, contact the Bluepes engineering team to discuss your specific environment and what a structured approach would look like.
Boomi is a trademark of Boomi, LP. Bluepes is an independent software consulting company. We are not affiliated with, endorsed by, or certified by Boomi, LP.
FAQ
Interesting For You
Why businesses are rethinking their integration strategy
Most IT teams don't notice integrations until something breaks at the worst possible moment. A new CRM rolls out, and three weeks later someone in finance discovers that customer data hasn't been syncing. An ERP upgrade ships on schedule and quietly disables five automated workflows that nobody documented. Revenue numbers look wrong in the dashboard because two systems are still running on different update cycles. This article is for CTOs, IT Directors, and VP Engineering roles who suspect their current integration architecture costs more to maintain than it should — in engineering hours, in delayed releases, and in recurring data quality incidents. Next — a clear breakdown of where standard approaches fail, what modern platforms actually offer, and how companies in healthcare, e-commerce, and finance are handling this shift in practice. Business integration modernization — replacing a fragmented collection of point-to-point connections with a centralised, scalable architecture — has become a priority for companies that have grown past their original tech stack. The pressure isn't coming from trend reports; it's coming from the compounding overhead of keeping legacy connections alive as systems multiply.
Read article

Cloud transformation in regulated industries: integration that holds up under scrutiny
When a hospital IT director evaluates a new integration platform, the first question is rarely "how fast can we deploy?" It's "what happens if this fails an audit?" That distinction shapes every architectural decision in industries where data handling is not just a technical concern — it's a legal one. This article is for IT Directors and CTOs in healthcare, financial services, and legal tech who are evaluating cloud integration options for environments where compliance is non-negotiable. Next — a practical look at what makes Boomi a platform that clients in regulated industries choose, and how Bluepes, as an independent integration consulting company, approaches these projects. Cloud integration for regulated industries means more than connecting APIs. It means building data flows that can be audited, reversed, restricted, and documented at any point — across systems that were never designed to talk to each other. Boomi addresses this by building compliance logic into the platform itself, rather than requiring teams to layer it on afterward. That design assumption is the main reason it comes up frequently in regulated industry evaluations.
Read article

Hybrid Integration Architecture with Boomi: Connecting Cloud and On-Prem Systems Without Disruption
Most enterprise environments are not fully in the cloud, and for good reason. ERP systems, compliance-sensitive databases, and internally hosted applications carry years of business logic that cannot be lifted and shifted without serious risk. The real architecture challenge is not choosing between cloud and on-prem — it is building a bridge between them that holds under production load. Bluepes is an independent software consulting company that works with Boomi as one of our integration platforms. Hybrid architecture is among the most frequent scenarios our clients bring to us. This article is for IT Directors and CTOs at mid-market companies who already operate mixed environments and need a clear picture of how hybrid integration actually works — the components involved, the security model, and where things break when the architecture is designed carelessly. Hybrid integration connects cloud services with on-premises systems through a runtime layer that handles data exchange, transformation, and orchestration. Neither environment needs to change its core structure — the integration layer abstracts the differences between them.
Read article